How to Spy Cell Phone Without Accessing Phone

3 Methods to Hack WhatsApp on Samsung phones
October 18, 2018
How to track cheating spouse on cell phone
October 23, 2018How to Spy Cell Phone Without Accessing Phone
Get the best Way to Spy Cell Phone without Accessing Phone
Smartphones have played a vital role in connecting the world like never before. Along with their multiple pros, you will accept that there are a handful of cons associated with them with which you are not aware. One of the biggest drawbacks behind using these smartphones is the uncertainty factor which exposes the community of smartphone users to considerable risks that are the product of this internet world. Due to this non-transparency, people looked for ways to seek substantial transparency in their lives. This gave way to the emergence of phone spy software. With the emergence of these spy software, it is now possible to spy cell phone without accessing phone from anywhere. As now the technology has advanced, the approach of such spying has shifted from traditional to modern. In the earlier days the phone was spied without the usage of any technology, it was a manual task and demanded physically accessibility to the phone which is being targeted. The risks of being caught were huge which caused a fear amongst hackers and their hacking purpose was not resolved wholly.
Imagine a situation when you are spying on your disloyal spouse and he catches you red-handed. That’s what exactly happened while using the traditional methods. But now there are a variety of phone spying tools which are completely reliable and secured.

Get the best Way to Spy Cell Phone without Accessing Phone
So, let’s get started to know more about this subject.
How to spy on cell phones without installation of the spying software on the target device: for iPhone
iOS is the second largest operating system in the world. It works only on Apple products, iPhone and iPad. This operating system is characterized by a special iCloud feature. iCloud can be termed as a loophole in iPhone and iPads because unknowingly it lays down a secretive path that takes you directly into the device. Yes, iCloud is a storage space in iOS devices which opens up several ways for a user to spy on the devices without installing any spying software. If the device belongs to your kids, spouses or employees then to figure out the Apple ID and password of the device is not really a difficult task. Once you have found out the ID and password, you need to enable iCloud backup and signup yourself on the spying software’s website. It depends on the software you choose, every software comes up with its own procedures and guidelines.
How to spy on a device without having access to it: Android
Android dominates majority of the world’s smartphone market. The most difficult thing while dealing with this operating system is remote installation of phone spy software. It does not allow you to download any monitoring spy software despite of working with different cloud storages. So, the only option with which a user is left with is persuading the owner of the device to click on the installation link to the spy software. This might be done with a wise use of the art of trickery.
Spy Cell Phone Apps that help you in spying devices without gaining access to them
Way 1: Using SpyZee App
Way 1: Using SpyZee App
SpyZee is one of the leading and popular spying phone apps in the market. The salient feature of this app is its easy installation and operations. Another reason to opt for this app is that it does not require any specialized knowledge and experience. It supports all versions of iOS and Android devices.
Some of the key features of this app are
- Tracks Communication: To thoroughly spy a device, you obviously need to track the communication data of the targeted device such as SMS, calls, messages on their social media handles. With the help of SpyZee, you can easily track and monitor any kind of communication between the device and external party.
- Tracks Location: SpyZee allows a user to track the GPS location of the target device from anywhere. It has the capability to deliver live and real-time location to the user.
- Keylogger: SpyZee imbibes a keylogger function which tracks every keystroke such as alphabets, numbers, buttons that are made on the target device. It captures all the communication that takes place on the device.
- Records Sound: The most fascinating feature of this app is its ability to switch on the device’s mic at any point of time without sending a prior intimation to the user of the device.
- Miscellaneous Other Feature: It has certain other salient characteristics such as the ability to track and record all the calls that are diverted to the device, the ability to track social media activities, the ability to monitor browsing history and download history which keeps you updated about what kind of content is being viewed by the device.
If these features fulfill your requirements, you may get started by installation of SpyZee software remotely.
Way 2: Using TheTruthSpy

Way 2: Using TheTruthSpy
Website: http://thetruthspy.com
It is considered as the preferable choice for Android and other operating system. It assures deriving all the vital information relating to the target device within a short time frame. You can also retrieve those information that was once deleted from the target device. If the owner clears the browser history you have also the power to retrieve that data. This app enables you to track real time location of the target device which bestows you with a degree of control over the user.
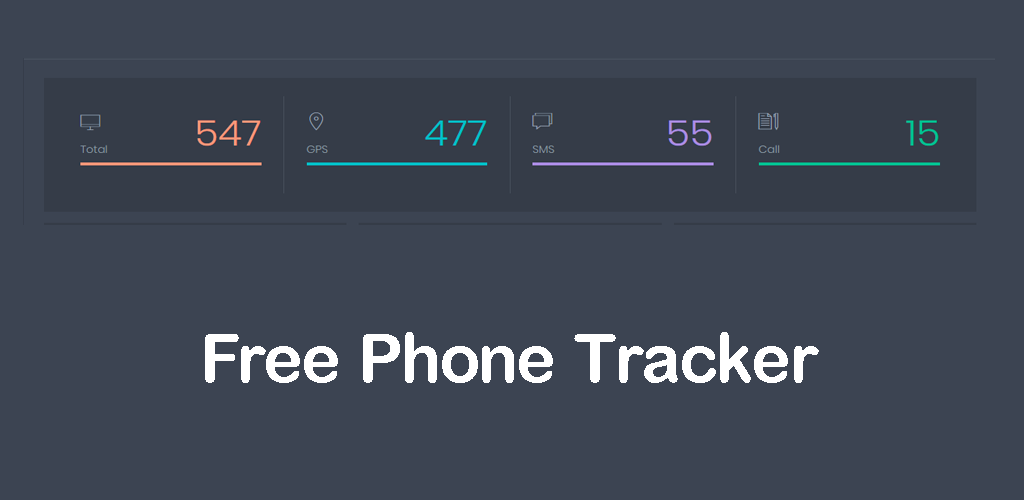
Way 3: Using Phone Tracker
Way 3: Using Phone Tracker
Website: https://phonetracking.net
It is a software application which is designed to spy on Android and iPhone devices without actually accessing the devices. To use this app, you need to start with configuration of the app and the app starts doing its work. It tracks all the conversation whether past or present on the targeted device. It logs all the information which the user delivers or receives through messages. Phone Tracker works in stealth mode which makes it non-traceable by the spied device. Another feature of this app is that you can heard over the live conversation of the target device as a third party. It can also track online activities on the user’s social media platforms such as Facebook, WhatsApp, and etc. This app works in background of the device in such a way that it keeps its identity unrevealed. It is only when a code is displayed directing itself to the control panel that the app may become detectable.
How to choose the best monitoring spy software program
There are a variety of spy software program available on the play store which have their own unique features and functions. It’s you who has to wisely choose the best one from the long list of applications. It is advisable that you go for that software which is commonly used and reviewed on the play store. You need to be cautious while choosing any spy software as there are many fake apps which claim to possess all the features which the other leading apps originally possess. Therefore you should learn beforehand about the apps and their functionalities before simply installing them. Secondly the thing which should fascinate you towards any app should be its efficiency. Sometimes, you may get confused between two or more apps, but at the end you need to choose anything that fits your requirements, purpose and compatibility.
Conclusion
To walk with this fast-paced world, you need to adopt technology and its advances. It is high time that you opt for modern methods to spy a cell phone without accessing it. These modern methods are nothing but the technological advances in the form of Spy Software programs such as TheTruthSpy, SpyZee, Phone Spying, GuestSpy and More. The software programs function by remotely establishing a connection with the monitoring devices. Once that remote connection has been set, any vital information relating to the target device may accessed by the person who is operating the software.
Precaution
If you are using a phone that you may make you suspicious about usage of any such spy software programming, it is recommended that you change your phone by switching to another number as sometimes executing a factor reset may not be enough to permanently remove the virus out of your device.



